PhantomRPC: Critical Windows RPC Vulnerability Enabling SYSTEM-Level Access
A newly identified vulnerability named PhantomRPC exposes a serious architectural weakness in the Windows Remote Procedure Call (RPC) mechanism. This flaw enables attackers to escalate privileges to SYSTEM-level access, potentially affecting all versions of Windows.
The research was presented by Haidar Kabibo from Kaspersky at Black Hat Asia 2026 on April 24, 2026. Notably, no patch has been released by Microsoft so far.
What Makes PhantomRPC Different
Unlike typical vulnerabilities, PhantomRPC is:
Not a memory corruption bug
Not a single-component flaw
Instead, an architectural design issue in how Windows RPC handles unavailable servers
The vulnerability exists in how the RPC runtime (rpcrt4.dll) manages connections when a target RPC server is offline or disabled.
When a high-privileged process attempts to connect to such a server, the system fails to verify the legitimacy of the responding endpoint.
This creates an opportunity for attackers.
How the Attack Works
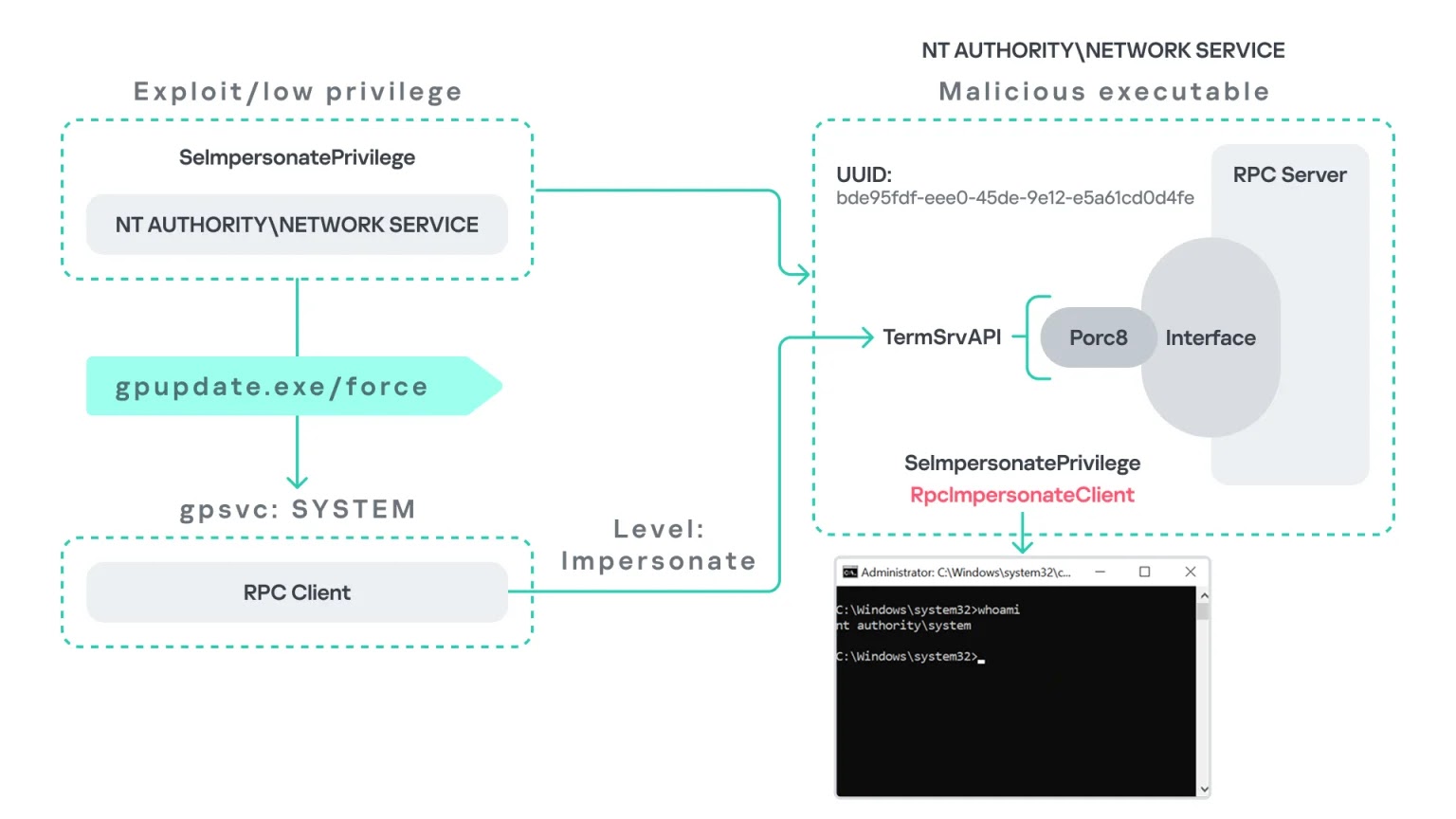
An attacker with a low-privileged account (e.g., NT AUTHORITY\NETWORK SERVICE) can:
Create a malicious RPC server
Mimic a legitimate RPC endpoint
Intercept incoming requests from privileged processes
The attack leverages the RpcImpersonateClient API, allowing the malicious server to:
Assume the identity of the connecting client
Escalate privileges to Administrator or SYSTEM level
Five Confirmed Exploitation Paths
Researchers identified five real-world attack scenarios:
gpupdate.exe Coercion
Running gpupdate /force triggers a SYSTEM-level RPC call. If the target service is disabled, the attacker intercepts it.
Microsoft Edge Startup
Microsoft Edge triggers RPC calls at launch, allowing silent privilege escalation.
WDI Background Service
The Diagnostic System Host (WdiSystemHost) automatically makes RPC calls every 5–15 minutes — no user action required.
ipconfig.exe + DHCP Client
Running ipconfig.exe can be exploited if DHCP services are disabled.
w32tm.exe (Windows Time Service)
Exploits a missing named pipe endpoint to impersonate privileged users.
Microsoft’s Response
The vulnerability was reported to the Microsoft Security Response Center on September 19, 2025.
Microsoft classified it as moderate severity, stating:
The attack requires SeImpersonatePrivilege
This privilege is already available to certain service accounts
As a result:
No CVE was assigned
No patch is planned currently
Recommended Security Measures
Until a fix is released, organizations should:
Monitor RPC activity using ETW logs (look for RPC_S_SERVER_UNAVAILABLE errors)
Enable critical services (like TermService) to prevent endpoint hijacking
Restrict SeImpersonatePrivilege to only essential processes
Avoid granting this privilege to third-party or custom applications
Conclusion
PhantomRPC highlights a deeper issue within Windows architecture rather than a simple bug. Because it leverages legitimate system behavior, it is harder to detect and mitigate.
Organizations should act proactively by strengthening monitoring, tightening privilege controls, and reviewing RPC exposure across systems.
Source: Cyber Security News – “New Windows RPC Vulnerability Lets Attackers Escalate Privileges Across All Windows Versions”
