New Phishing Campaign Uses Fake Event Invitations to Steal Credentials
A large-scale phishing campaign has been quietly targeting organizations across the United States using fake event invitations as bait. Instead of relying on suspicious attachments or obvious scam links, attackers are luring victims with what appear to be legitimate party or gathering invitations.
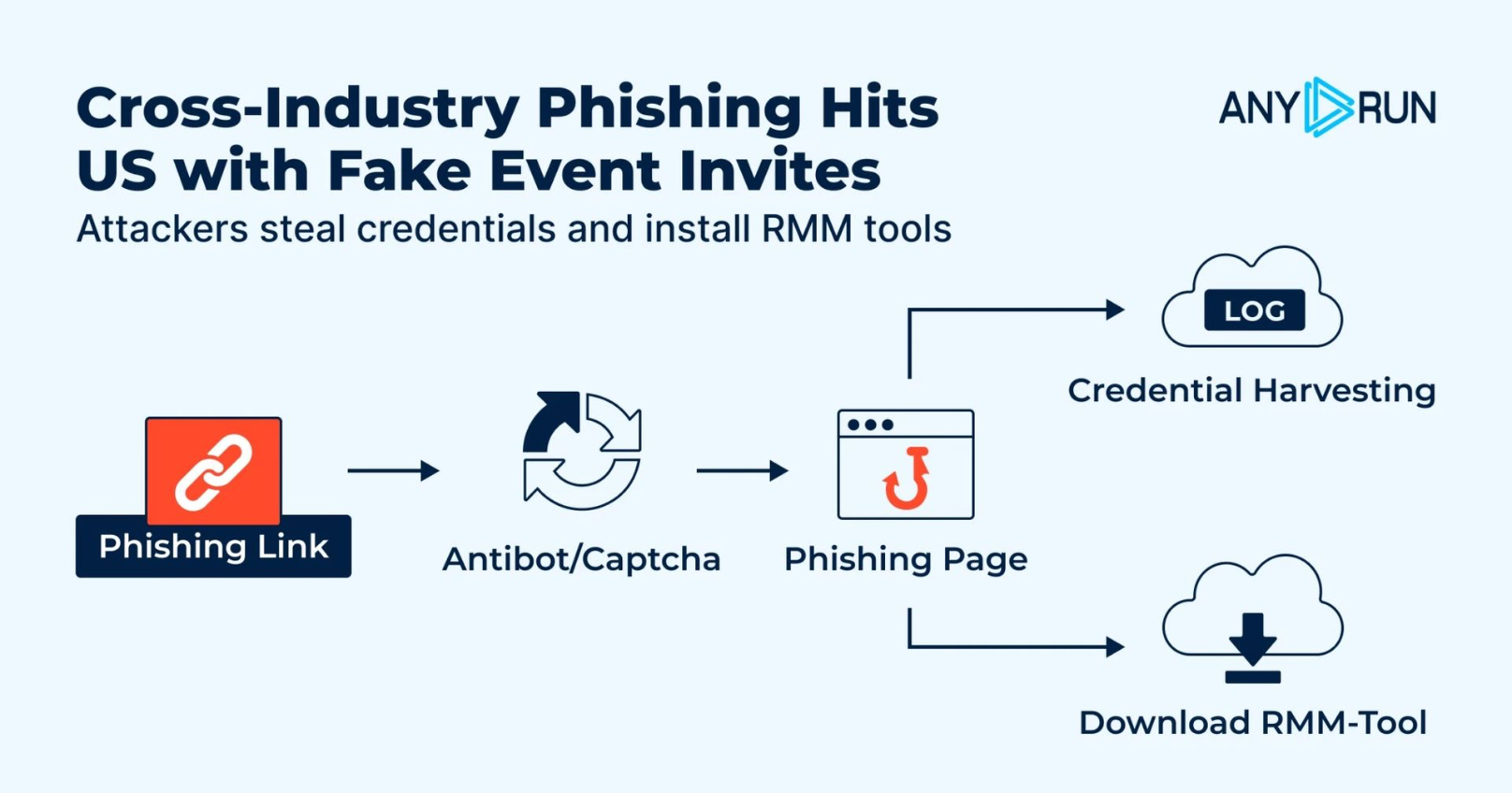
Once clicked, these links redirect users to phishing pages designed to steal login credentials, intercept one-time passcodes (OTPs), or install remote management software on the victim’s device.
What makes this campaign particularly dangerous is how normal the initial interaction appears. Victims receive an invitation, click the link, pass through a CAPTCHA verification page, and are presented with a polished-looking event website. Nothing in this process immediately raises suspicion, allowing the attack to progress unnoticed.
By the time any malicious activity becomes visible, whether through stolen credentials or unauthorized remote access tools running silently in the background,the attackers have often already established access to the system.
Researchers at ANY.RUN were among the first to uncover the full scope of the campaign. On April 22, 2026, analysts identified phishing operations specifically targeting email service credentials, with certain variants also delivering remote management software.
By April 27, nearly 160 suspicious links had been submitted to ANY.RUN’s sandbox environment, leading researchers to identify approximately 80 phishing domains. Most of these domains were registered under the .de top-level domain beginning in December 2025.
The industries most affected by this phishing campaign include Education, Banking, Government, Technology, and Healthcare. These sectors depend heavily on email communication systems and remote administration tools, making them attractive targets for attackers attempting to blend malicious activity into normal operations.
A single compromised login credential within any of these environments can potentially provide access to sensitive internal systems, confidential communications, financial data, or administrative infrastructure far beyond a single email account.
The campaign also appears to be designed for large-scale deployment. Researchers believe the threat actors are using a reusable phishing toolkit that allows them to rapidly generate new event-themed phishing pages with minimal effort. Some elements of the fake websites suggest possible AI-assisted content generation, enabling attackers to expand operations quickly while maintaining a consistent structure across multiple phishing domains.
Phishing Attack Weaponizing Event Invitations
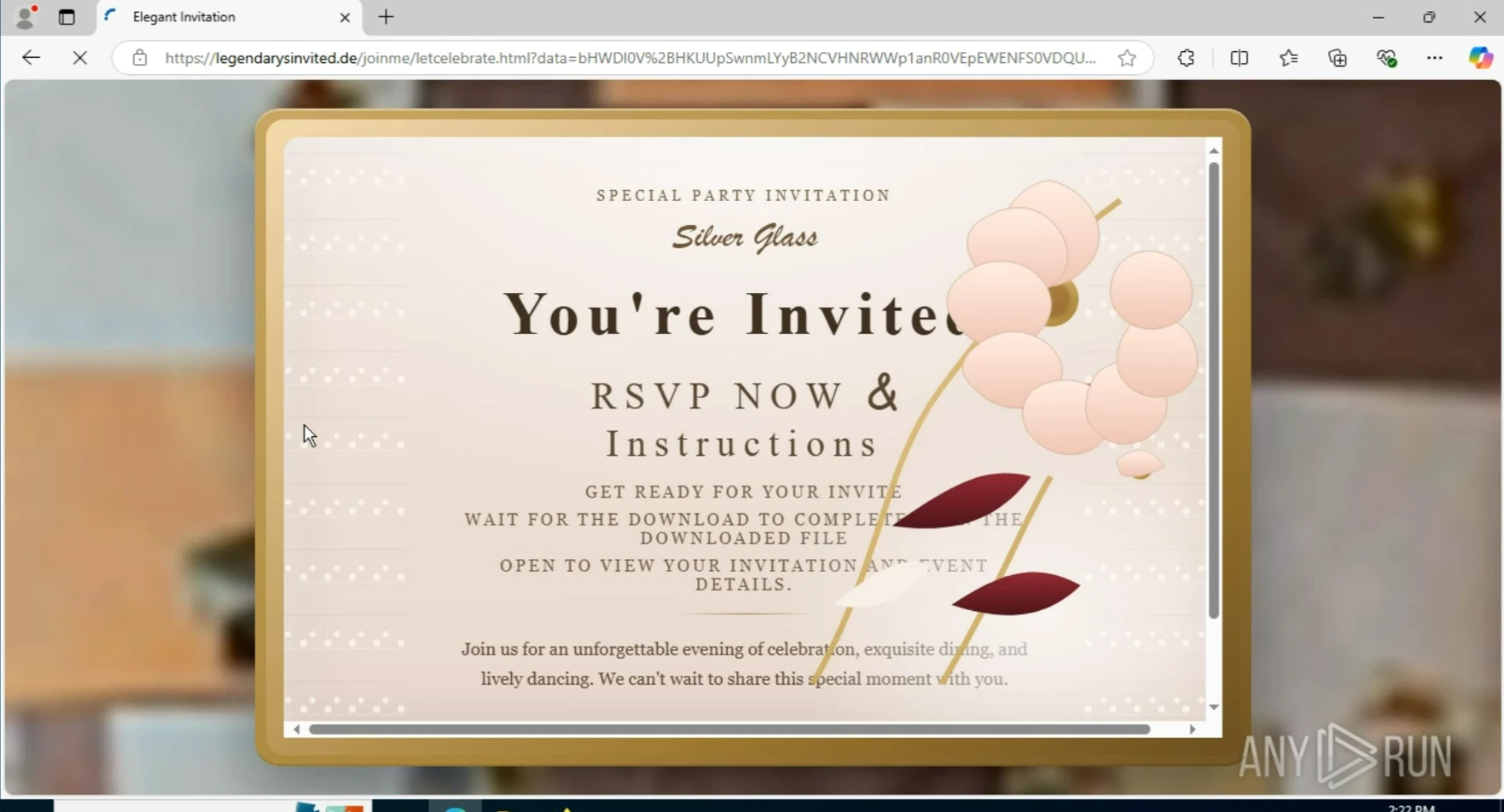
The attack typically begins with a simple invitation link sent to the victim. After clicking the link, users are redirected through a CAPTCHA verification page, most commonly delivered through Cloudflare, which helps make the phishing page appear more legitimate and trustworthy.
Once the CAPTCHA step is completed, the victim is redirected into one of two attack paths depending on the phishing variant being used.
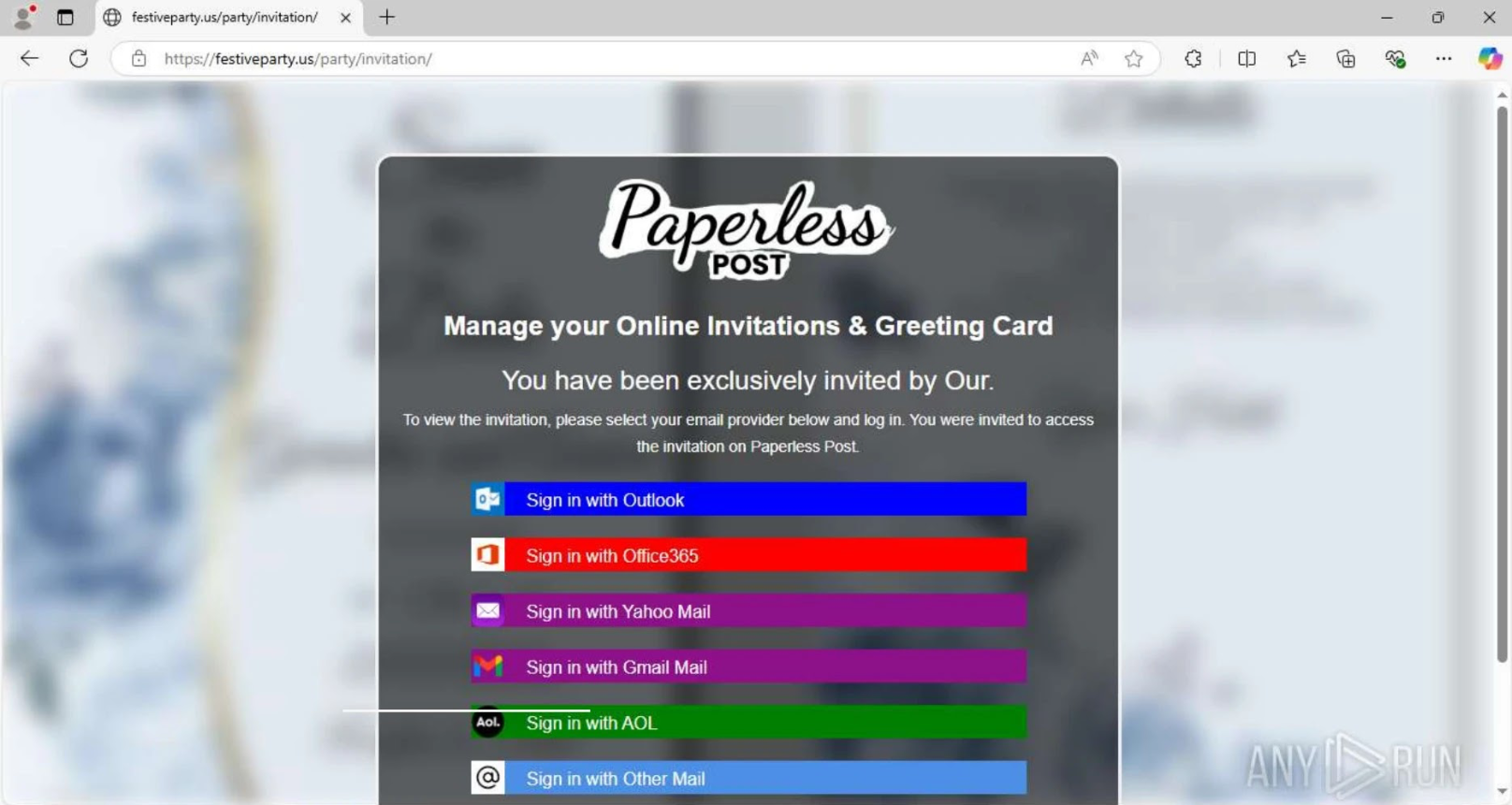
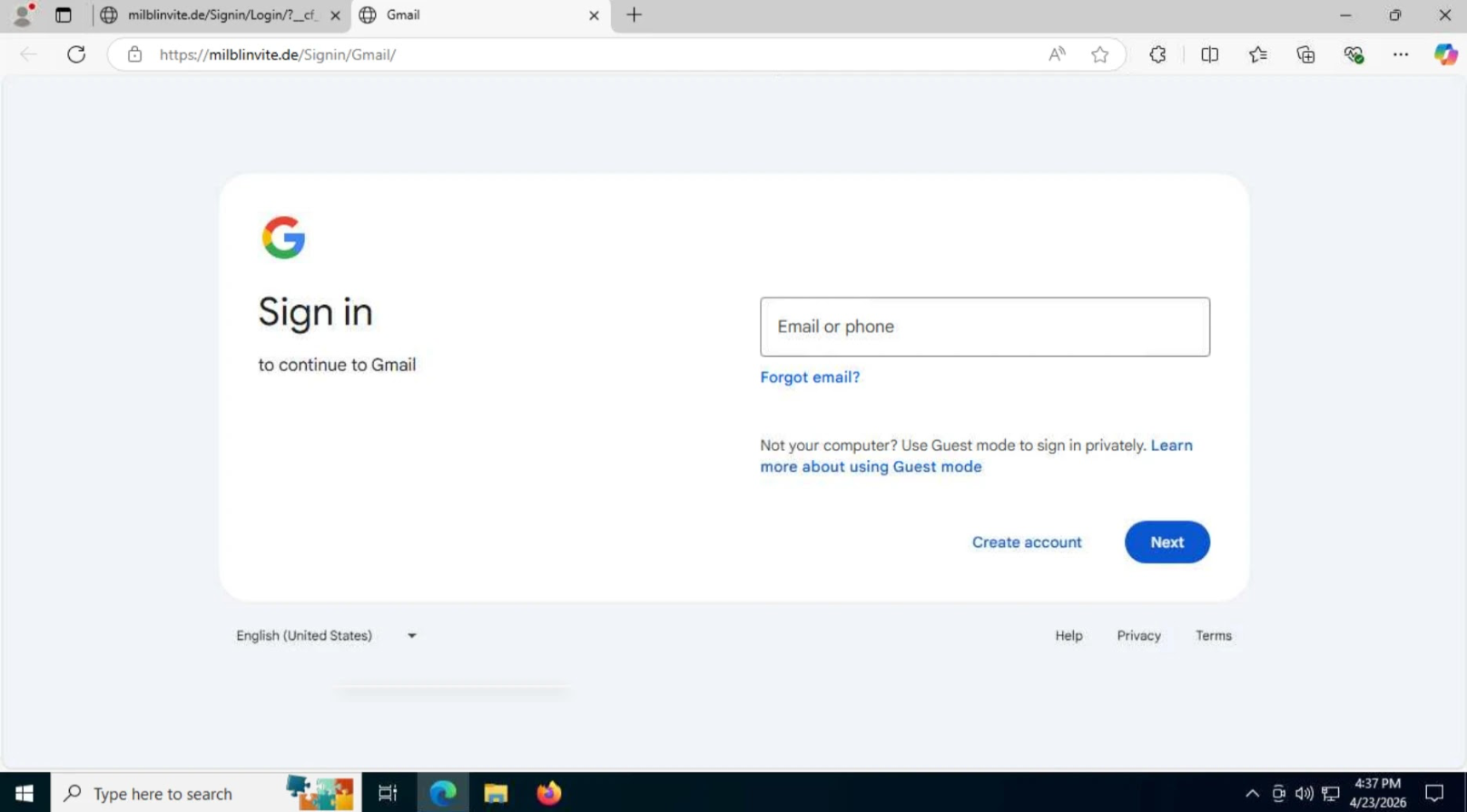
In the credential theft variant of the campaign, victims are presented with a sign-in page asking them to choose their preferred email service provider. When users select Google, they are redirected to a highly convincing fake Google authorization page designed to closely mimic the legitimate login experience.
Once credentials are entered, the information is transmitted to attacker-controlled server endpoints through POST requests, including paths such as /pass.php and /mlog.php. This allows attackers to silently capture usernames, passwords, and potentially additional authentication data without immediately alerting the victim.
For all other services, the page collects the email and password, then deliberately shows an “Incorrect Password” message to push the user into entering their details a second time, capturing both attempts. Once the user submits an OTP code, that too is silently forwarded to the attacker.
In the remote management delivery version, the fake invitation page initiates a download of a legitimate remote tool such as ScreenConnect, ITarian, Datto RMM, ConnectWise, or LogMeIn Rescue. Some pages include a download button, while others begin the download automatically with no further action needed. Because these are real, widely used tools, security software may not treat the installation as a threat.
How Security Teams Can Reduce the Risk
Security teams can use shared infrastructure patterns to hunt for related domains before an incident takes shape. All phishing pages in this campaign follow a predictable request chain: a GET request to the root, followed by requests to /favicon.ico, /blocked.html, and an image path matching /Image/*.png. Analysts can run the query url:"/blocked.html" AND url:"/favicon.ico" and url:"/Image/*.png"url:"/blocked.html" AND url:"/favicon.ico" and url:"/Image/*.png" in threat intelligence platforms to surface connected domains.
Beyond hunting, organizations benefit most from getting visibility earlier in the chain, before credentials are used or a remote tool gains a foothold. Safely analyzing suspicious links in a sandboxed environment lets teams confirm whether a page is a fake invitation, a credential form, or an RMM delivery page before any user data is at risk.
When teams can observe the full behavior of a link during investigation, they can contain the threat much faster and avoid the costly uncertainty that comes with reacting too late.
Indicators of Compromise:-
| Type | Indicator | Description |
|---|---|---|
| URL Pattern | hxxps://<phish_site>/<url-pattern>/Image/office360.png | Phishing page icon path for Office 365 branding |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/Image/office.png | Phishing page icon path for Office branding |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/Image/yahoo.png | Phishing page icon path for Yahoo branding |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/Image/google.png | Phishing page icon path for Google branding |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/Image/aol.png | Phishing page icon path for AOL branding |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/Image/email.png | Phishing page icon path for generic email branding |
| URL Pattern | hxxps://<phish_site>/blocked.html | Shared blocked page across all campaign domains |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/processmail.php | Credential submission endpoint (non-Google flow) |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/process.php | OTP submission endpoint |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/pass.php | Google credential login endpoint |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/mlog.php | Google credential password endpoint |
| URL Pattern | hxxps://<phish_site>/<url-pattern>/check_telegram_updates.php | Visitor ID exfiltration endpoint (Google flow) |
| File Hash (SHA-256) | 887bc414bdb32b83dcfccdd3c688e90d9a87a0033e3756a840f9bdd2d65… | office360.png icon used in phishing pages |
| File Hash (SHA-256) | 6eaa0a448f1306bcf4159783eeafe5d37243bd8ca2728db7d90de192924… | office.png icon used in phishing pages |
| File Hash (SHA-256) | 4c373bc25cb71dbb75e73b61dff25aa184be8d327053a97202a6b1a5919… | yahoo.png icon used in phishing pages |
| File Hash (SHA-256) | a838f99537d35e48e479a34086297f76db5d3363b0456f23d10d308f0d3… | google.png icon used in phishing pages |
| File Hash (SHA-256) | 8e94c18bbcad0644c4b04de4356fe37da9996fdf1c99bc984ba819862a9… | aol.png icon used in phishing pages |
| File Hash (SHA-256) | 9a53e032a6e3e79861d28568c3b6ffc97f4f3c1d3af65a703ec129664205… | email.png icon used in phishing pages |
| Domain | festiveparty[.]us | Event-themed phishing domain observed in campaign |
| Domain | getceptionparty[.]de | Event-themed phishing domain observed in campaign |
| Domain | celebratieinvitiee[.]de | Event-themed phishing domain observed in campaign |
| TI Hunting Query | url:”/blocked.html” AND url:”/favicon.ico” and url:”/Image/.png” | Query to find related phishing domains in ANY.RUN TI Lookup |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Source Credit
Source: Cyber Security News
Read more: https://cybersecuritynews.com/new-phishing-attack-weaponizing-event-invitations/
